1. nginx配置https
如果不需要https访问,可以跳过此步骤,直接使用http即可,或者阅读下一节配置CDN加速。
1.1 方式一:freessl申请证书
直接登录https://freessl.cn申请免费证书即可,网站都有操作指导。
原先想申请Let’s Encrypt证书,但是一直失败,原因未知。改为申请TrustAsia免费双域名证书,有效期1年,申请成功。

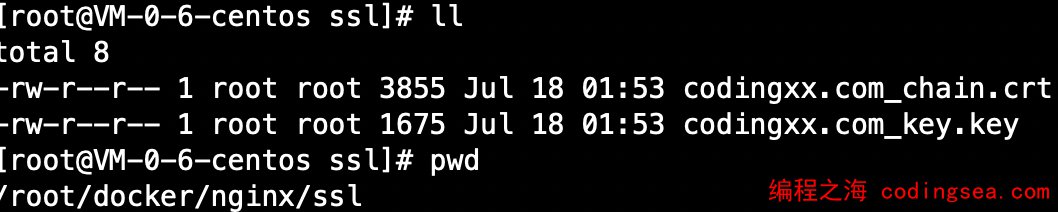
上传证书到云主机/root/docker/nginx/ssl目录下:
1.2 方式二:certbot命令行申请证书
下面是折腾命令行申请Let’s Encrypt证书的步骤,dns校验一直不通过,后面尝试成功了再更新:
# 1. 安装certbot
yum install -y epel-release
yum install -y snapd
systemctl enable --now snapd.socket
ln -s /var/lib/snapd/snap /snap
snap install --classic certbot
ln -s /snap/bin/certbot /usr/bin/certbot
certbot certonly --manual --preferred-challenges=dns --email yufei_email@163.com -d *.codingsea.com,codingsea.com
#出现如下提示后,先去域名解析里面添加TXT记录,等几分钟再按Enter继续,否则会失败。
#Please deploy a DNS TXT record under the name:
#_acme-challenge.codingsea.com.
#with the following value:
#_TERSm4CcA5Qy8GlVDSTvxN_dqV-my0BkAY_nflAj9w
#- - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - - #- - - - - -
#Press Enter to Continue
1.3 配置nginx使用https
# 1. 生成 dhparam.pem 文件, 在命令行执行任一方法:
# 方法1: 很慢
openssl dhparam -out /root/docker/nginx/ssl/dhparam.pem 2048
# 方法2: 较快
# 与方法1无明显区别. 2048位也足够用, 4096更强
openssl dhparam -dsaparam -out /root/docker/nginx/ssl/dhparam.pem 2048
# 2. 生成nginx配置文件
cat <<EOF >/root/docker/nginx/conf/conf.d/codingsea.com.conf
# 不发送Nginx版本号
server_tokens off;
# 将所有 http 跳转至 https
server {
if (\$host = www.codingsea.com) {
return 301 https://codingsea.com\$request_uri;
}
set \$flag 0;
if ( \$host != www.codingsea.com ) {
set \$flag "\${flag}1";
}
if ( \$host != codingsea.com) {
set \$flag "\${flag}2";
}
if (\$flag = "012") {
return 404;
}
listen 80 default_server;
listen [::]:80 default_server;
server_name codingsea.com;
return 301 https://\$host\$request_uri;
}
server {
if (\$host = www.codingsea.com) {
return 301 https://codingsea.com\$request_uri;
}
set \$flag 0;
if ( \$host != www.codingsea.com ) {
set \$flag "\${flag}1";
}
if ( \$host != codingsea.com) {
set \$flag "\${flag}2";
}
if (\$flag = "012") {
return 404;
}
listen 443 ssl http2;
listen [::]:443 ssl http2;
server_name codingsea.com;
location / {
proxy_pass http://wp;
proxy_http_version 1.1;
proxy_cache_bypass \$http_upgrade;
proxy_set_header Upgrade \$http_upgrade;
proxy_set_header Connection "upgrade";
proxy_set_header Host \$host;
proxy_set_header X-Real-IP \$remote_addr;
proxy_set_header X-Forwarded-For \$proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto \$scheme;
proxy_set_header X-Forwarded-Host \$host;
proxy_set_header X-Forwarded-Port \$server_port;
}
# certs sent to the client in SERVER HELLO are concatenated in ssl_certificate
ssl_certificate /etc/ssl/codingsea.com_chain.crt;
ssl_certificate_key /etc/ssl/codingsea.com_key.key;
# 启用 session resumption 提高HTTPS性能
# http://vincent.bernat.im/en/blog/2011-ssl-session-reuse-rfc5077.html
ssl_session_cache shared:SSL:50m;
ssl_session_timeout 1d;
ssl_session_tickets off;
ssl_dhparam /etc/ssl/dhparam.pem;
# 禁用 SSLv3(enabled by default since nginx 0.8.19) since it's less secure then TLS http://en.wikipedia.org/wiki/Secure_Sockets_Layer#SSL_3.0
ssl_protocols TLSv1 TLSv1.1 TLSv1.2;
# ciphers chosen for forward secrecy and compatibility
# http://blog.ivanristic.com/2013/08/configuring-apache-nginx-and-openssl-for-forward-secrecy.html
ssl_ciphers 'ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:DHE-RSA-AES128-GCM-SHA256:DHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA:ECDHE-RSA-AES256-SHA384:ECDHE-RSA-AES128-SHA:ECDHE-ECDSA-AES256-SHA384:ECDHE-ECDSA-AES256-SHA:ECDHE-RSA-AES256-SHA:DHE-RSA-AES128-SHA256:DHE-RSA-AES128-SHA:DHE-RSA-AES256-SHA256:DHE-RSA-AES256-SHA:ECDHE-ECDSA-DES-CBC3-SHA:ECDHE-RSA-DES-CBC3-SHA:EDH-RSA-DES-CBC3-SHA:AES128-GCM-SHA256:AES256-GCM-SHA384:AES128-SHA256:AES256-SHA256:AES128-SHA:AES256-SHA:DES-CBC3-SHA:!DSS';
# 启用服务器端保护, 防止 BEAST 攻击
# http://blog.ivanristic.com/2013/09/is-beast-still-a-threat.html
ssl_prefer_server_ciphers on;
# 启用 ocsp stapling (网站可以以隐私保护、可扩展的方式向访客传达证书吊销信息的机制)
# http://blog.mozilla.org/security/2013/07/29/ocsp-stapling-in-firefox/
ssl_stapling on;
ssl_stapling_verify on;
ssl_trusted_certificate /etc/ssl/codingsea.com_chain.crt;
# 启用 HSTS(HTTP Strict Transport Security) https://developer.mozilla.org/en-US/docs/Security/HTTP_Strict_Transport_Security
# 避免 ssl stripping https://en.wikipedia.org/wiki/SSL_stripping#SSL_stripping
# 或 https://hstspreload.org/
add_header Strict-Transport-Security "max-age=31536000; includeSubdomains; preload";
# replace with the IP address of your resolver
resolver 8.8.8.8 8.8.4.4;
}
EOF
# 3. 重启服务
docker-compose restart
2. 测试网站访问
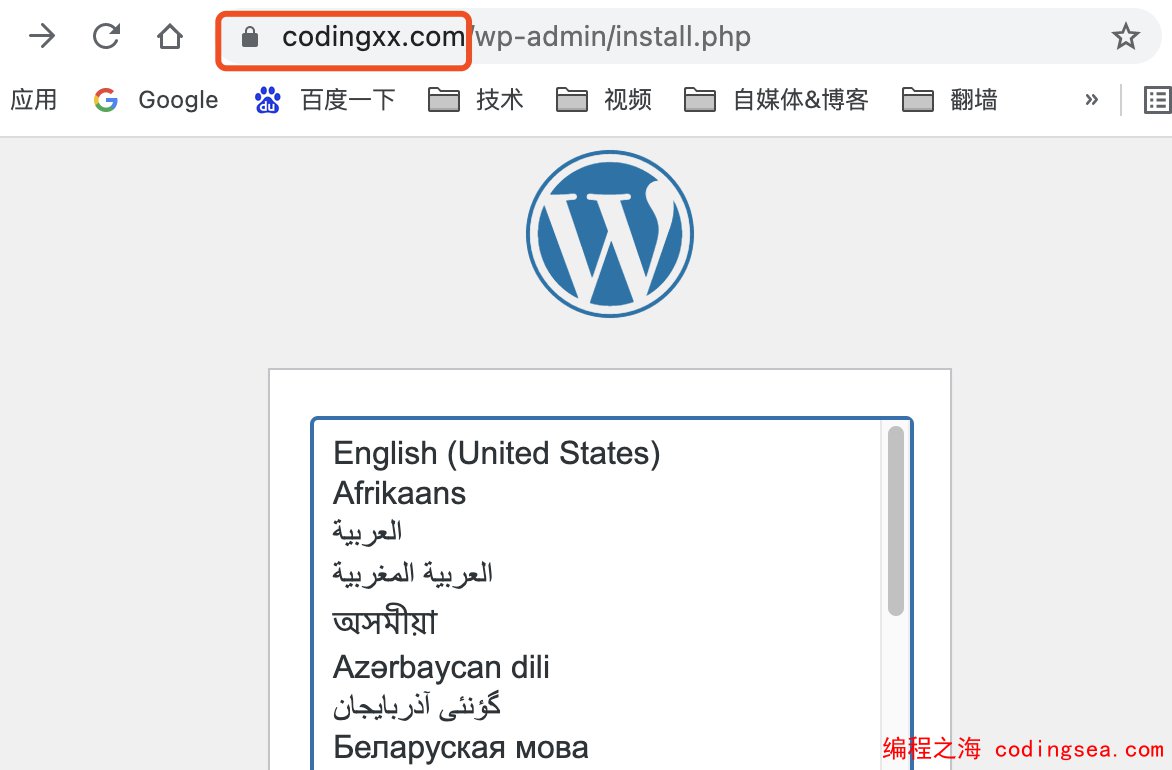
如果需要使用CDN加速,可以阅读下一节配置CDN加速。到时需要删除上面添加的A记录,攻击者便无法从域名获取真实的主机IP,有利于保护主机安全。

编程之海 版权所有丨如未注明,均为原创丨转载请注明转自:https://codingsea.com/wordpress-nginx-https/






